This how-to will walk you through setting up automated certificate installation and renewal with SSL.com for Apache and Nginx with the ACME protocol and Certbot client.
sudo privileges on your web server to follow these instructions.You can use many other ACME clients, including Kubernetes cert-manager, with SSL.com’s ACME service.
acme4j client can now use SSL.com ACME services on this repository: https://github.com/SSLcom/acme4j
Please refer to your software provider’s documentation for instructions for other non-Certbot ACME clients.
Install Certbot and Retrieve ACME Credentials
- SSH into your web server.
- Make sure that a current version of Certbot, along with the Apache and Nginx plugins, are installed on your web server:
- If you have snapd installed, you can use this command for installation:
sudo snap install --classic certbot
- If
/snap/bin/is not in yourPATH, you will also need add it or run a command like this:sudo ln -s /snap/bin/certbot /usr/bin/certbot
- If you have snapd installed, you can use this command for installation:
- Retrieve your ACME credentials from your SSL.com account:
- Log into your SSL.com account. If you are already logged in, go to the Dashboard tab.
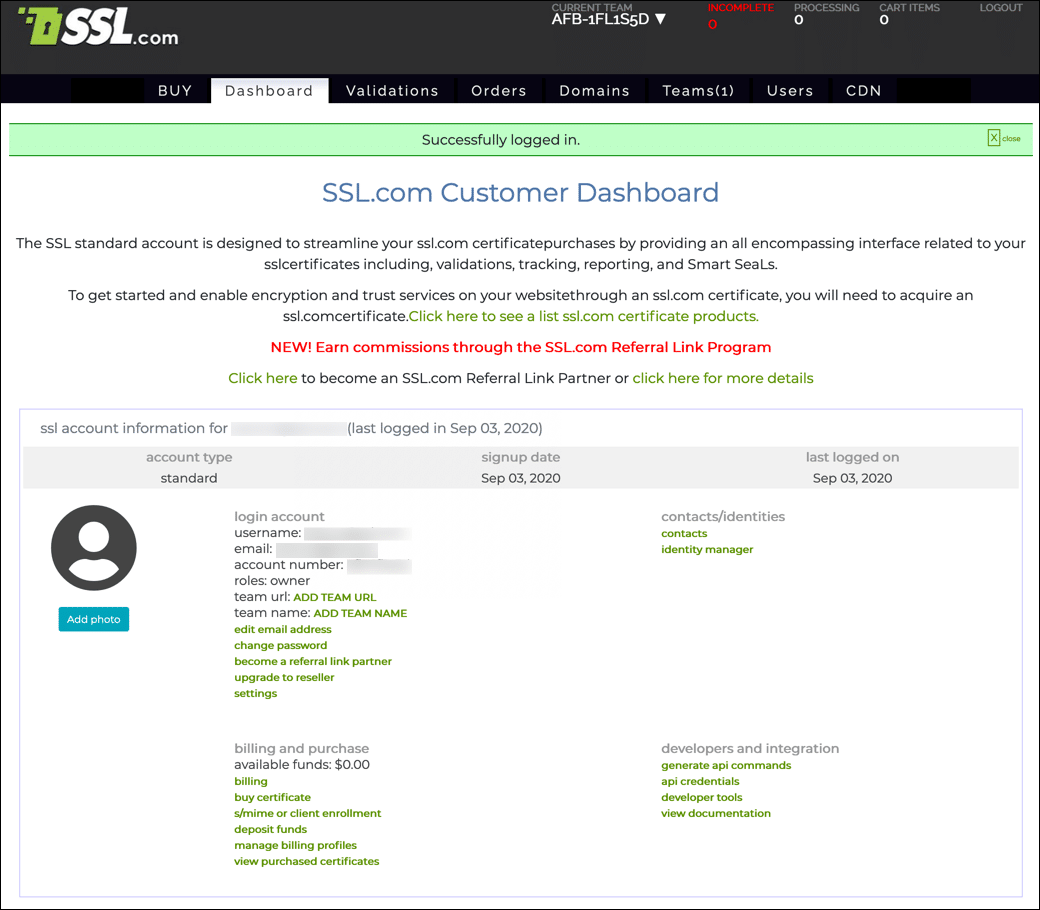
- Click api credentials, located under developers and integration.
- You will need your Account/ACME Key and HMAC Key to request certificates. Click the clipboard icon () next to each key to copy the value to the clipboard.
- Log into your SSL.com account. If you are already logged in, go to the Dashboard tab.
Apache Installation and Automation
Use a command like this to install on Apache. Replace values in ALL CAPS with your actual values:
sudo certbot --apache --email EMAIL-ADDRESS --agree-tos --no-eff-email --config-dir /etc/ssl-com --logs-dir /var/log/ssl-com --eab-kid ACCOUNT-KEY --eab-hmac-key HMAC-KEY --server https://acme.ssl.com/sslcom-dv-rsa -d DOMAIN.NAME
Breaking the command down:
sudo certbotruns thecertbotcommand with superuser privileges.--apachespecifies to install certificates for use with Apache.--email EMAIL-ADDRESSprovides a registration email address. You may specify multiple addresses, separated by commas.--agree-tos(optional) agrees to the ACME subscriber agreement. You can omit this if you want to agree interactively.--no-eff-email(optional) indicates that you do not want share your email address with the EFF. If you omit this you will be prompted with the option to share your email address.--config-dir /etc/ssl-com(optional) sets the configuration directory.--logs-dir /var/log/ssl-com(optional) sets the directory for logs.--eab-kid ACCOUNT-KEYspecifies your account key.--eab-hmac-key HMAC-KEYspecifies your HMAC key.--server https://acme.ssl.com/sslcom-dv-rsaspecifies SSL.com’s ACME server.-d DOMAIN.NAMEspecifies the domain name that the certificate will cover.
-d DOMAIN.NAME option multiple times in your command to add domain names to your certificate. Please see our information on certificate types and billing to see how different combinations of domain names map to SSL.com certificate types and their corresponding pricing.certbot command, ACME account info will be stored on your computer in the configuration directory (/etc/ssl-com in the command shown above. On future runs of certbot, you can omit the --eab-hmac-key and --eab-kid options because certbot will ignore them in favor of the locally stored account info.
If you need to associate your ACME certificate orders for the computer with a different SSL.com account, you should remove this account information from your computer with the command sudo rm -r /etc/ssl-com/accounts/acme.ssl.com (or, if you omitted the optional --config-dir option, sudo rm -r /etc/letsencrypt/accounts/acme.ssl.com).
You should see output like this after you run the command:
Saving debug log to /var/log/ssl-com/letsencrypt.log Plugins selected: Authenticator apache, Installer apache Obtaining a new certificate Performing the following challenges: http-01 challenge for DOMAIN.NAME Waiting for verification... Cleaning up challenges Created an SSL vhost at /etc/apache2/sites-available/DOMAIN-le-ssl.conf Deploying Certificate to VirtualHost /etc/apache2/sites-available/DOMAIN-le-ssl.conf Enabling available site: /etc/apache2/sites-available/DOMAIN-le-ssl.conf Redirecting vhost in /etc/apache2/sites-enabled/DOMAIN.NAME.conf to ssl vhost in /etc/apache2/sites-available/DOMAIN-le-ssl.conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations! You have successfully enabled https://DOMAIN.NAME - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Certbot will also create a crontab file like this for automated non-interactive renewal of any certbot-installed certificate expiring within 30 days:
$ cat /etc/cron.d/certbot # /etc/cron.d/certbot: crontab entries for the certbot package # # Upstream recommends attempting renewal twice a day # # Eventually, this will be an opportunity to validate certificates # haven't been revoked, etc. Renewal will only occur if expiration # is within 30 days. # # Important Note! This cronjob will NOT be executed if you are # running systemd as your init system. If you are running systemd, # the cronjob.timer function takes precedence over this cronjob. For # more details, see the systemd.timer manpage, or use systemctl show # certbot.timer. SHELL=/bin/sh PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin 0 */12 * * * root test -x /usr/bin/certbot -a \! -d /run/systemd/system && perl -e 'sleep int(rand(43200))' && certbot -q renew
Nginx Installation and Automation
For Nginx, simply substitute --nginx for --apache in the command shown above:
sudo certbot --nginx --email EMAIL-ADDRESS --agree-tos --no-eff-email --config-dir /etc/ssl-com --logs-dir /var/log/ssl-com --eab-kid ACCOUNT-KEY --eab-hmac-key HMAC-KEY --server https://acme.ssl.com/sslcom-dv-rsa -d DOMAIN.NAME
Force Renewal Manually
If you wish to manually renew a certificate before expiry is imminent, use this command:
certbot renew --force-renewal --cert-name DOMAIN.NAME
SSL.com provides a wide variety of SSL/TLS server certificates for HTTPS websites.